The number of integrated OT and IT systems is growing around the entire world, which is most often explained by the need to improve the operational efficiency of the business. For example, a SCADA system now not only controls oil production and transportation, but also provides the necessary data for the systems which calculate the pricing of goods and form invoices. Collecting and processing a large amount of data allows companies to more accurately predict not only the volumes of oil production, but also the expected revenues in the future. However, the integration of OT and IT systems brings more than just benefits. The disadvantages of such systems include an increased likelihood of cyberattacks on OT security systems.
The use of outdated software further exacerbates this complex problem. You can learn about this fr om the interview with the CEO of IDC Taiwan in the video. Hackers can exploit Windows vulnerabilities and attack inadequately protected systems.
As more cybersecurity incidents occur in OT systems, business owners and regulators are looking to find solutions that will improve industrial cybersecurity and enable businesses to function properly.
In this article, we will introduce the concept of Defense-in-depth, a deep multi-layered protection, which allows companies use existing network infrastructure to build network protection, as well as discuss the features of industrial intrusion prevention systems.
Layered security concept
To improve cybersecurity, it is important to understand how various industrial systems communicate within the infrastructure and how they relate to IT systems. In the ideal scenario, each system, down to every individual module, should be separated fr om the others and have its own security policy that provides traffic filtering, user authentication and authorization. However, creating such security policies between each device becomes an unrealistic task, since it is expensive and often negatively affects the efficiency of network communications. That is why cybersecurity engineers recommend dividing the OT system into several main zones with different security policies, which will allow a client to find the optimal balance between costs and an acceptable level of risk.
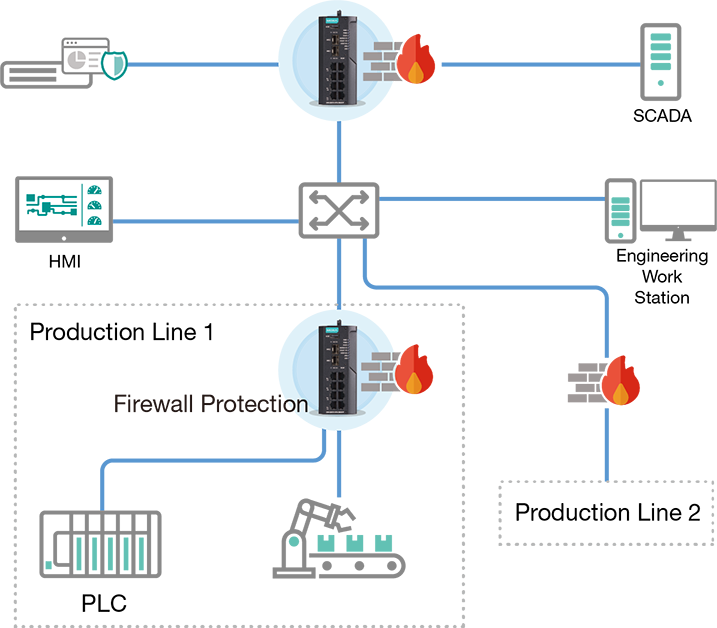
An example of building a multi-layered security boundary to protect production lines from various cyber incidents.
The Defense-in-depth approach is recommended by the cybersecurity standard IEC 62443, which is widely used in various industries and ensures the continuity of technological processes.
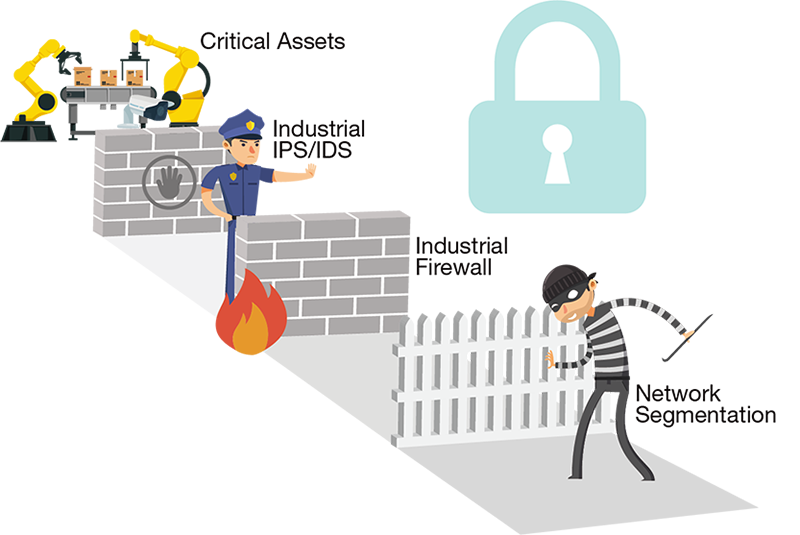
Securing critical assets is one of the most important tasks in an enterprise because they play a central role in business. Because of this, it is advisable to take additional security measures, for example, establish multiple layers of protection to better protect critical assets.
The Defense-in-depth security concept is based on the creation of multiple layers of protection to enhance the security of the entire system.
How to build a layered security system
There are several approaches to building a multilevel security system, let’s take a look at the most popular ones.
Physical network segmentation
With physical segmentation of a network, we have 2 physically isolated networks from each other. This provides a good level of security, however, in modern companies such a solution is rather difficult to organize due to the increasing business requirements and the complexity of operation.
Data link segmentation (OSI Layer 2/3)
Since industrial control systems could have been built several decades ago, one of the main requirements for building a security system is the ability to use the existing infrastructure. One of the commonly used approaches for separating data transmission channels is to configure virtual local area network (VLAN), which is one of the built-in functions of managed Ethernet switches.
Some Ethernet switches have a built-in feature for creating access control lists (ACLs) at the port level, which can increase VLAN security as data arrives at the switch. An alternative solution is to deploy multiple firewalls, especially when it is necessary to handle traffic in Layer 3 networks.
Segmentation of networks at the packet inspection layer (OSI Layer 4-7)
Further network segmentation can be based on deep packet inspection (DPI). DPI provides granular control over network traffic and helps filter industrial protocols according to established requirements. For example, several devices operate on the same network that can communicate with each other. However, there may be a scenario wh ere the controller must communicate with the robotic arm only at certain times. This is wh ere DPI technology will help engineers set up deep security policies, allow execution of read/write commands at a specific time, or deny traffic from other directions.
Network micro-segmentation
In some situations, additional protection of critical assets is needed, and one way to achieve this goal is to apply network micro-segmentation and install an IPS (intrusion prevention system). Network micro-segmentation is especially useful for industrial networks when it is necessary to additionally protect a small section of the subnet.
Another advantage of this approach is that the IPS has a virtual patching functionality, which eliminates the risk of exploiting already known vulnerabilities. For example, some objects might be running Windows XP, for which Microsoft no longer releases security updates. At such a site, even though there are known vulnerabilities, it may not be appropriate to update the security system. In this you can find out how the virtual IPS security patch works.
Secure remote access
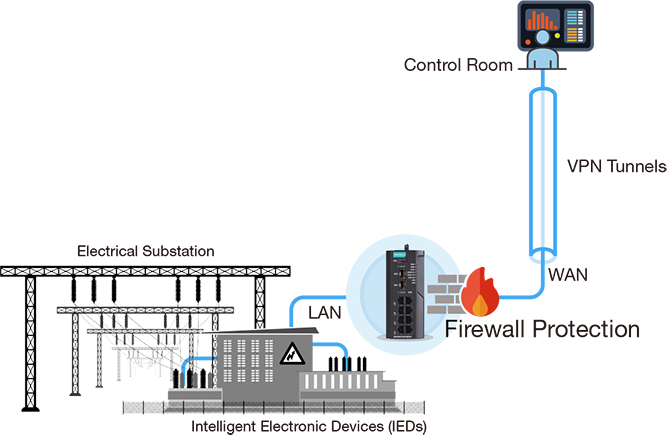
According to cybersecurity experts, poorly configured remote access protocols are used to spread malware or engage in unauthorized activity. As remote connections become more prevalent due to the need to improve efficiency and the need for quick troubleshooting, it is not surprising that creating security boundaries between objects is becoming more and more talked about. Instead of using software to create remote access, experts strongly recommend creating VPN tunnels to ensure reliable functioning of access control mechanisms.
Typical scenarios
Industrial production
Different production networks must be properly segmented to ensure the safety of the entire system. In addition, to ensure the availability and continuity of a control system, it is necessary to provide network redundancy. An example of such a scheme is shown below.

Safe substation monitoring
A power system that spans a vast area requires IEC 61850-certified VPN solutions to monitor remote intelligent electronic devices (IEDs). In addition, several layers of protection should be deployed at the substation to ensure cybersecurity and prevent loss of access to the facility.
Can all these requirements be combined in one device?
One of the options for such a device can be EDR-G9010. It is a universal firewall with NAT, VPN, switch and router functions. The EDR-G9010 will not only help improve cybersecurity, but will also leverage existing network infrastructure.

For further technical information, inquiries about offers or placement of orders, please contact our sales team at sales@ipc2u.com